
What Hash Format Are Modern Windows Login Passwords Stored In?
In this step-by-step guide, you will learn about the hash format in which modern Windows login passwords are stored in. As well as learn how to reset Windows login passwords using hash-cracking techniques.
There are multiple online guides on the same subject. But most of them are outdated or have irrelevant information. Outdated because Windows, with its regular updates, continuously changes the way passwords are stored in hashes.
So, we have ensured to update this guide and provide clear instructions to reset the Windows login password with hash. You will also find screenshots to understand each step better. Sometimes hashes cannot reset complex Windows passwords, so we also included how to reset Windows login passwords with the hash alternative.
Part 1. What Hash Format Are Windows Login Passwords Stored In?
The modern Windows login passwords are stored in the NTLM (NT Lan Manager). Initially designed for the Windows NT OS, NTLM is still used today in the latest Windows systems, like Windows 10 and Windows Server 2016.
NTLM is the format that Windows uses to store local user accounts and domain user accounts securely. But it is important to note that hashes alone are not considered a robust encryption method by Windows. That is why it uses additional security measures like salting the hashes to make it difficult for someone to crack the password.
You cannot derive the actual local user or domain user password using NTLM hash. Still, you can use it to compare with a user-supplied password and determine if the provided password is correct.
The earlier version of Windows used the LM (Lan Manager) hash format, like Windows NT 3.5, Windows 95, and Windows 98. LM is no longer used because of its simple encryption nature that can easily be cracked. It also had a limited character set, meaning even a dictionary attack could guess the password.
Part 2. How Are Passwords Stored in Windows?
The modern Windows login password is stored in hash formats. A hash is a one-way mathematical function that takes an input and creates a similar-size output. Windows stores login passwords in hashes because passwords are vulnerable to storing in plain text. Since the hash is a one-way function, it is impossible to reverse engineer the original password from the hash value.
For instance, when you create a new password on your Windows device, it is first created as a hash. The hash is stored in the Windows SAM database or Active Directory database. Windows stores the password in SAM if it is a local account and in Active Directory if it is a domain account password.
At the login screen, the password you enter is matched using an algorithm, and Windows gives you access to the account if the passwords match.
Part 3. How to Reset Windows Login Password with Hash
Hash is a one-way function and irreversible, and it will not reveal the actual password. However, it’s not foolproof. You can use tools to reset your Windows login passwords using a hash. And here are the two best tools to reset Windows password with hash:
Method 3.1. Using Cain
Cain and Abel is a free, Windows-based security tool designed for password recovery. You can use the program for various purposes, including password recovery, monitoring and analyzing network traffic, and perform other security-related tasks on the Microsoft Operating System. You can use Cain and Abel to perform dictionary, brute-force, or Rainbow Table attacks.
You can use Cain and Abel to recover passwords from various sources, including FTP, HTTP, IMAP, LDAP, POP3, SMTP, and more.
Given the straightforward and modern user interface, Cain and Abel allow even the least tech-literates to recover Windows login passwords conveniently.
How to use Cain and Abel to Reset the Windows Login Password With Hash?
Note: You can only use Cain and Abel if you can access other accounts on the same Windows computer. If you cannot access other accounts on the computer, use PassFab 4WinKey — the Hash Alternative method to reset your Windows login password.
Step 1. Download and Install the Cain and Abel program from the official website.
Note: Cain and Abel is an old password-recovery tool, and its official website has been shut down. You have to go to Webarchive.org and access the official site of Cain and Abel.
- You have to disable any running antivirus programs on the Windows computer. Additionally, you have to turn off the Windows firewall. You can scroll down to the FAQs section to learn how to turn off Windows Firewall.
- Once the Cain and Abel program is installed, click the Cracker tab.
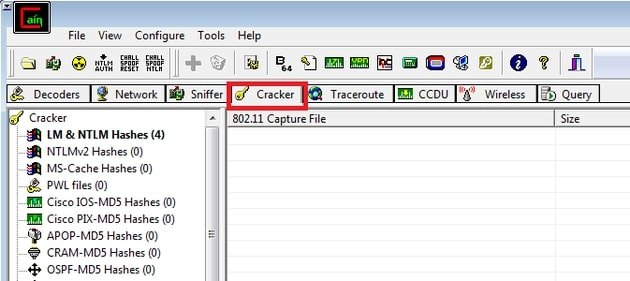
- From the left pane, choose LM & NTLM Hashes option from all the categories.
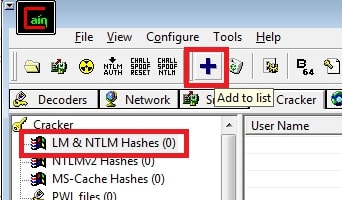
- Once you select the LM & NTLM Hashes category from the left pane, the + (blue) button in the main menu will be enabled.
- Click on the + (blue) button to import Hashes from the local system.
- From the left panel, click the “Cross” button in the upper toolbox.
- Click on the Import Hashes from Local System button in the succeeding windows and select Next.
- Once you click on the Next option, Cain and Abel will show all the software programs installed on the Windows computer.
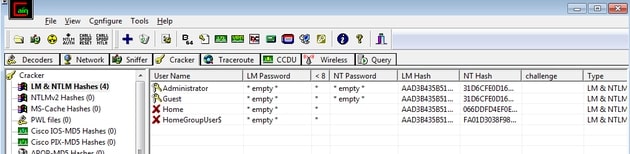
- Right-click on the username with which you want to reset the password.
- Wait for the password recovery process to complete and copy the Hashes under the LM Hashes.
- The cell that displays *empty* value has passwords.
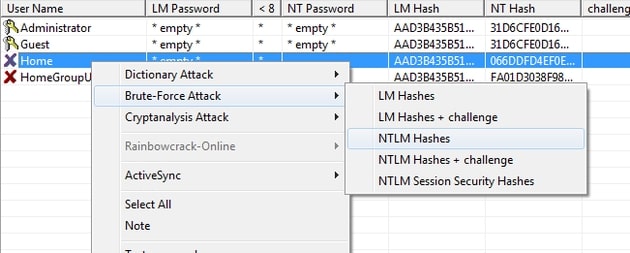
- Right-click on the User account and choose Brute Force Attack.
- From the drop-down menu, choose NTLM Hashes.
- Select a Charset to extract the Windows login password.
- Click the “Start” button.
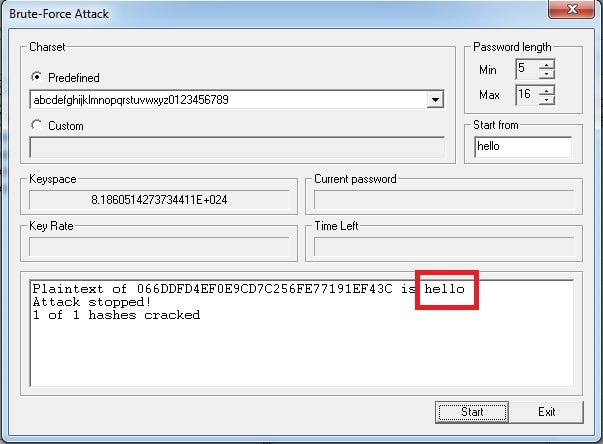
Wait for the password recovery process to complete. Once located, Cain and Abel will display the found password.
Method 3.2. Using Ophcrack
Another free and open-source Windows password cracking tool, Ophcrack, allows you to reset the Windows device by analyzing the encrypted password hashes stored in the Windows SAM (Security Account Manager). After locating the database stored in SAM, Ophcrack attempts to find the Windows password using precomputed Rainbow tables.
Here’s How to Use OPHCrack to Find Windows Password Via Hash Format
Note: Ophcrack only works on Local accounts on Windows computers. So, you cannot use the program to crack the Microsoft Login page.
Step 1. Download and Install Ophcrack.
Head over to https://ophcrack.github.io/ and download the latest version of the Ophcrack. Install the program and Agree to the Terms and Conditions when the software prompts it. Alternatively, you can download the Ophcrack program from SourceForge.
Note: You have to download the Ophcrack file on the locked computer via another Local or Admin account. Like Cain & Abel, Ophcrack does not allow you to recover the Windows password using another computer.

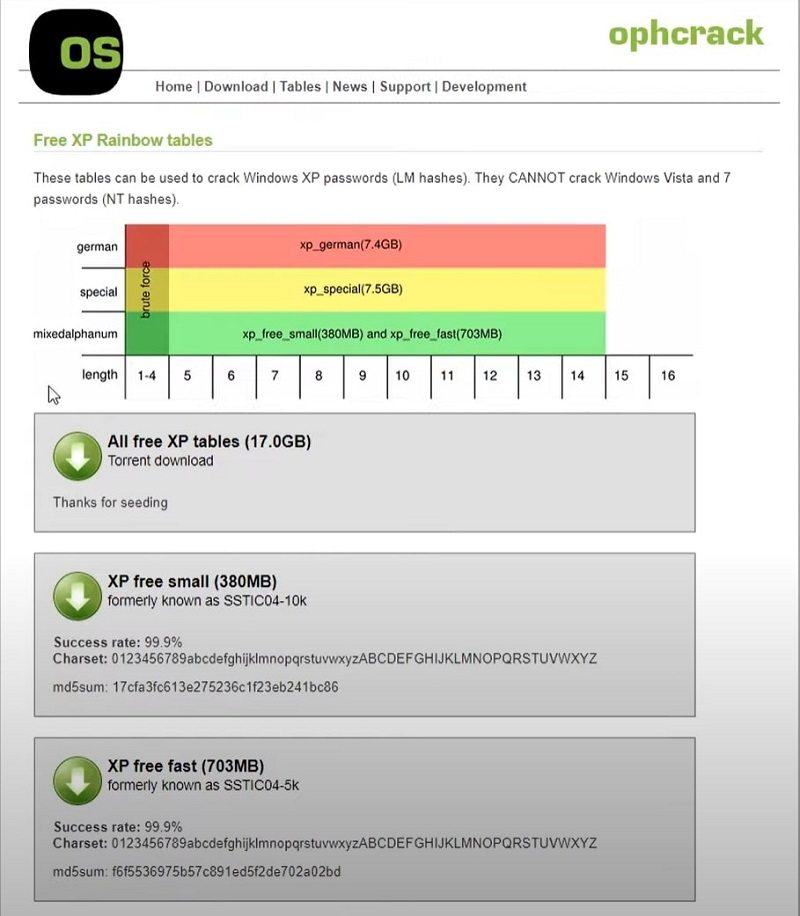
Click on the Tables option in the upper menu and download the Rainbow tables, depending on the Windows version. You can also download the Rainbow tables of other Windows versions if needed.
As mentioned, the hash format is a modern Windows login password stored in NT hashes. And the hash format of the older Windows login password is stored in LM Hashes. So, ensure to download the Rainbow tables accordingly.
Step 2. Download Transmission to download Rainbow Tables.
The above downloads are magnet links—and not actual files. To download the Rainbow tables, you have to download another tool called Transmission — a free BitTorrent client — to download Rainbow tables from a peer-to-peer network. It is important to note that Ophcrack does not store the actual Rainbow Tables on its website (no official site). So you have to rely on peer-to-peer seeding to download the Rainbow Tables to crack the password via hash format, which modern Windows computers are stored in.
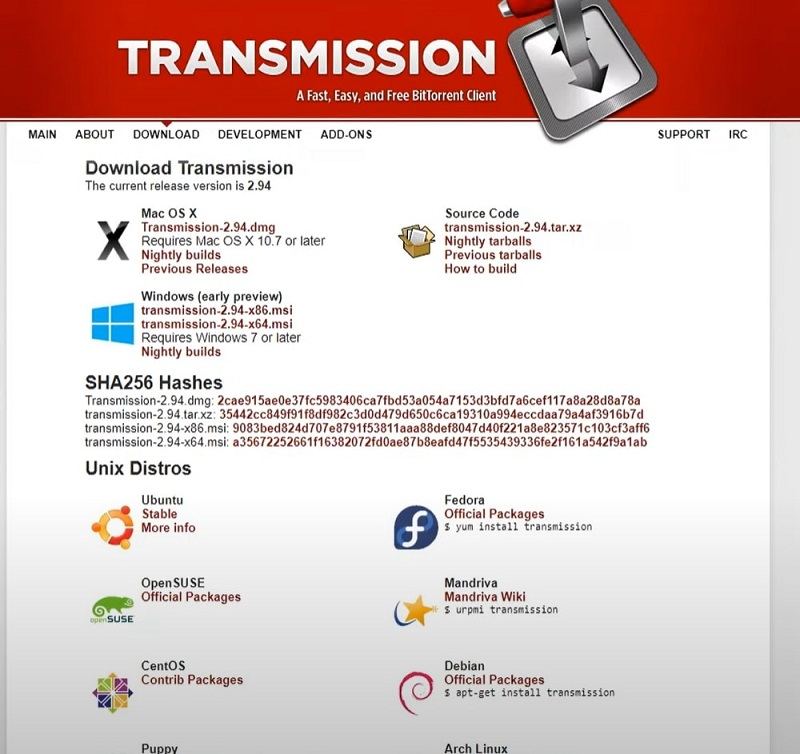
After downloading the Transmission for Windows, open the program (Transmission).
From the main menu, choose File. And Open to open the magnet links and download the Rainbow tables.
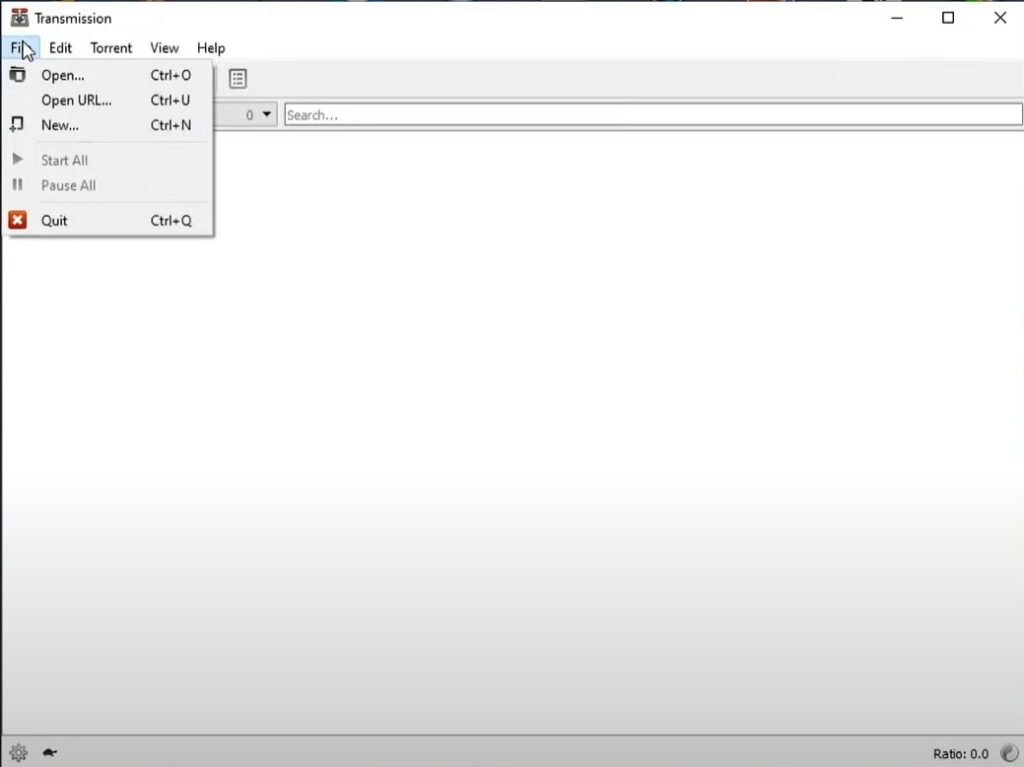
- Locate the desired magnet files using the File Manager.
- Click Open to allow peer-to-peer seeding.
- Wait for the download to complete. Depending on the internet connection speed and seed availability, it will take 2-8 hours to download all the Rainbow Tables required to crack the Windows password.
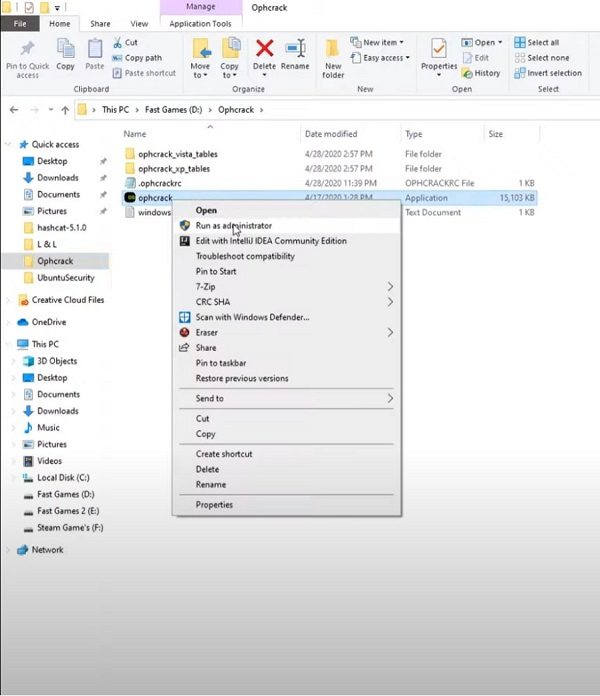
Step 3. Locate the Ophcrack application to find the Local user account password via Hash Format used by modern Windows login passwords.
- Right-click on the program and click on Run as administrator.
- After opening the program, click on Tables from the main menu options.
- Choose the desired Tables from the downloaded ones and click on Install. You have to manually install all the Rainbow Tables that you have downloaded.
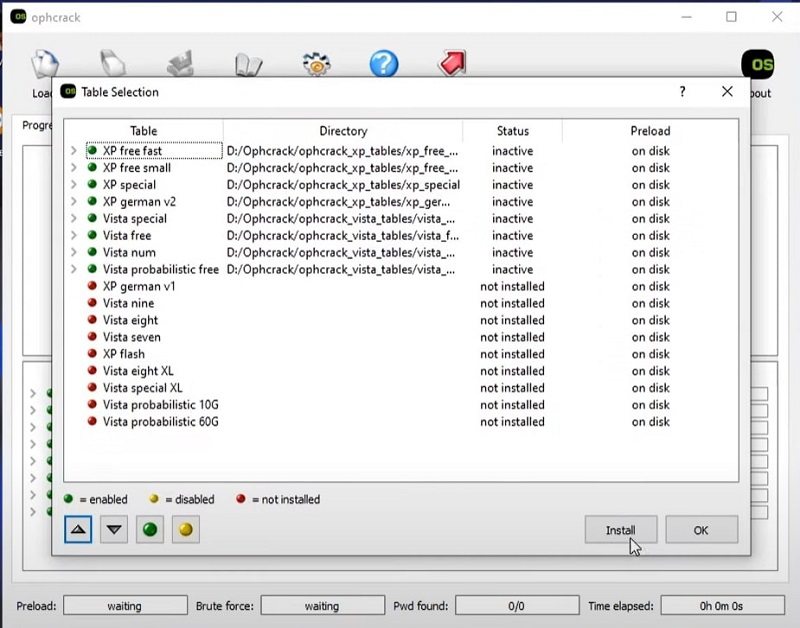
- Click on OK to start the installation and start the Windows password cracking via the Hash Format process.
- Wait for the Ophcrack program to complete the password cracking using Hash Format.
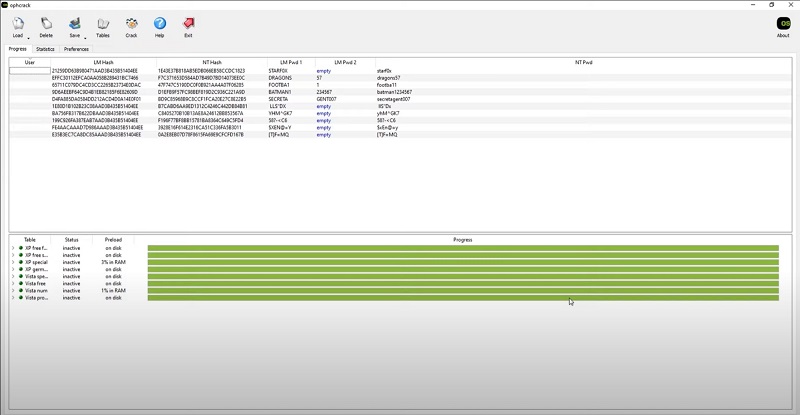
Once done, you can write down all the found passwords. And use them one by one to open the locked User account on Windows.
Well, now that you know about the Hash Format in which modern Windows login passwords are stored in, you can use the above methods to reset the Windows password.
Part 4. How to Reset Windows Login Password with Hash Alternative?
The problem with the above software is you must know the Hash used by the Windows computer to reset the Windows login password. And that requires you to have another Local or Admin account on the same computer. Many users may not have another User account, so the above two methods to reset Windows passwords might not work for them.
So what to do when you are locked out of your Windows account and do not have any other User account on the computer, and do not have access to the Hash? You can still reset your Windows password using third-party tools like PassFab 4WinKey.
Step 1. Create Windows Password Reset Disk
>> Get PassFab 4WinKey Coupon (30% OFF) <<
- Download and Install the PassFab 4WinKey on another Windows device.
- On the main interface, choose Start.
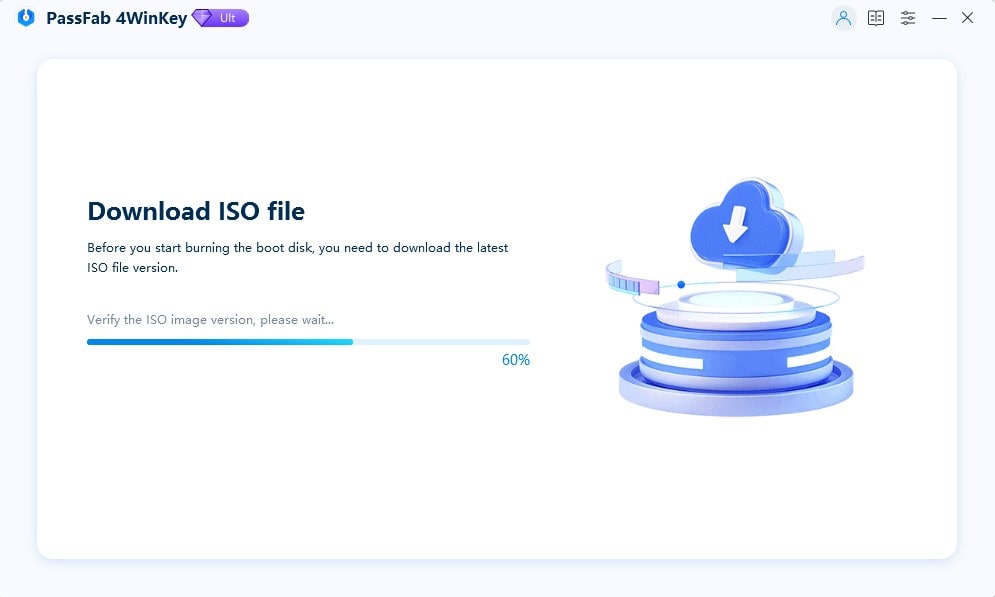
Wait for the 4WinKey to verify the ISO version and download the latest version.
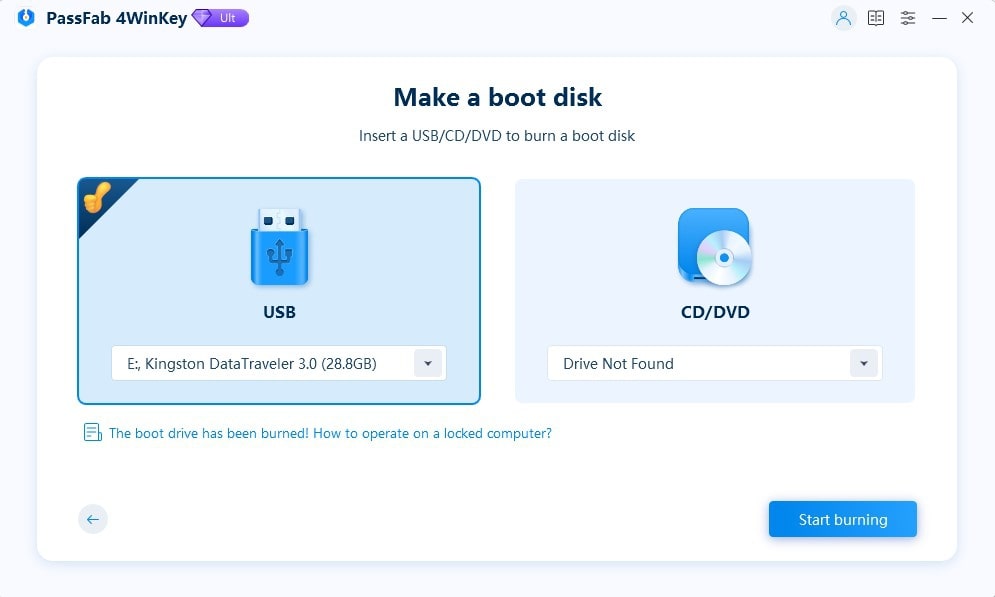
- Insert the bootable disk (USB Flash Drive or CD/DVD).
- Choose Start burning.
- Select the Next option.
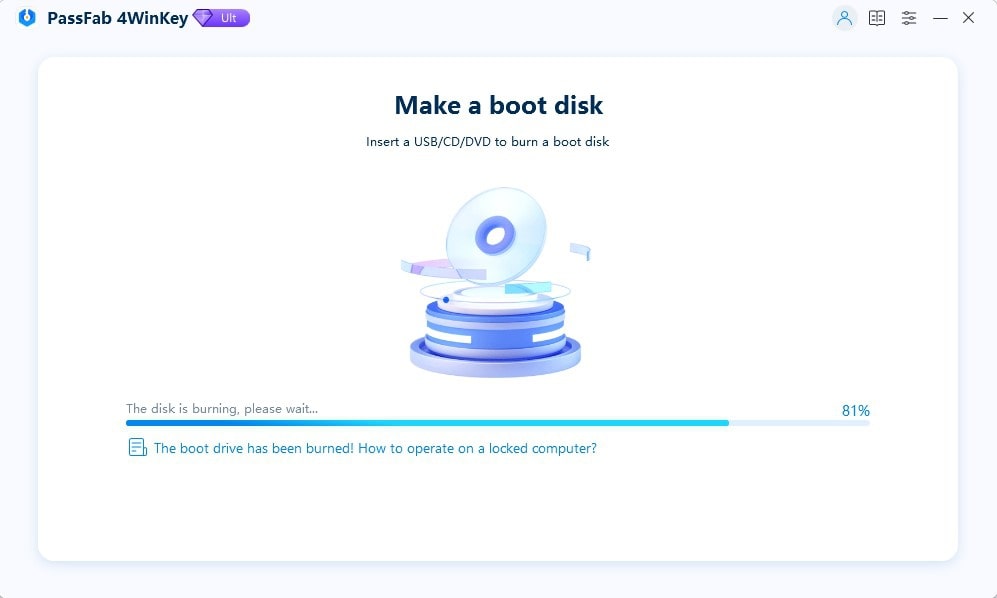
- Once you click on the Next option, PassFab 4WinKey will burn the inserted USB Flash drive or CD/DVD drive.
Step 2. Boot the locked Windows computer using a USB Flash drive or CD/DVD.
- Eject the USB drive or CD/DVD and insert it into the locked Windows computer.
- Turn on the computer and press the F12 or Esc button when you see the manufacturer’s logo.
(Note: F12 or Esc buttons are the most common buttons to enter the Boot menu. However, it differs from manufacturer to manufacturer. So, ensure to find the boot key from the internet beforehand.)
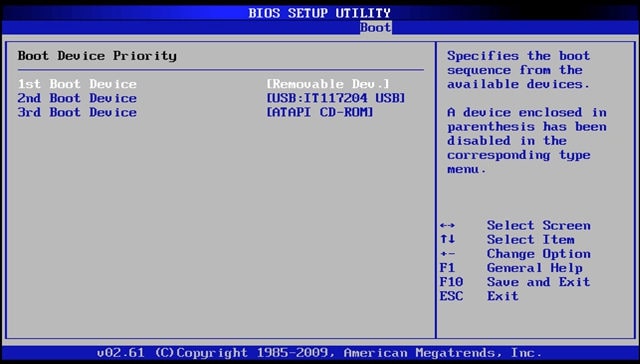
- Once you enter the Boot Setup Utility, choose the Boot Device Priority option. On some computers, the Boot menu does not support the mouse. So, you have to use the arrow buttons to navigate.
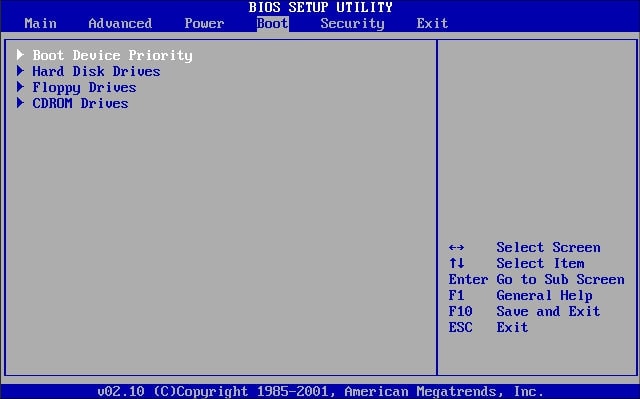
- In the Boot Device Priority menu, choose the inserted device and move it to the top. So, it is 1st Boot Device.
- Save the changes and exit the BIOS menu.
Step 3. Reset or Remove the Windows Account Login Password.
- Once you exit the BIOS menu, your Windows computer will restart again.
- After the restart, you will see a new interface instead of the regular login page.
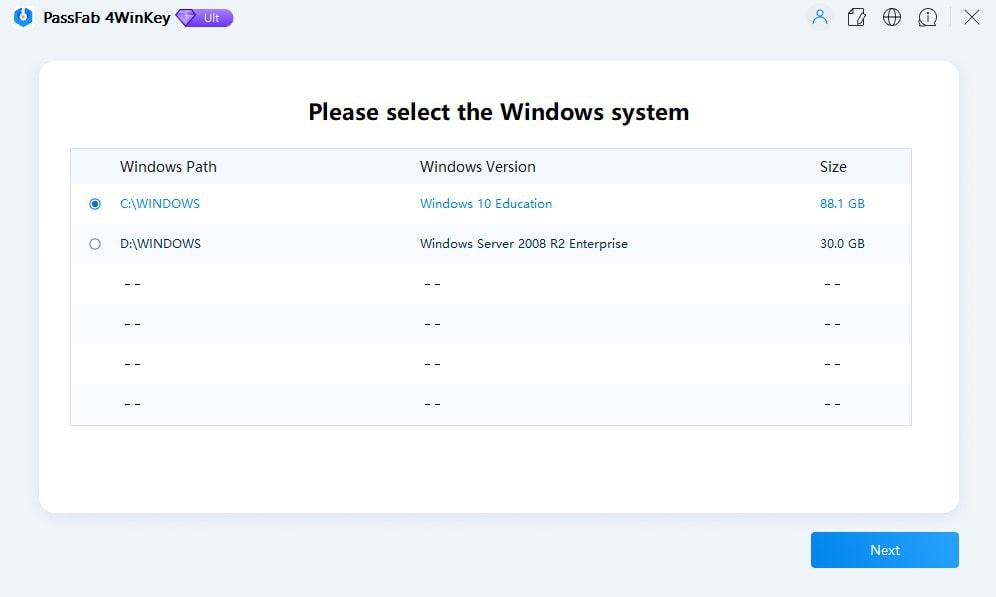
- Select the Windows version that is installed on the locked Windows device.
- On the PassFab 4WinKey interface, you will find four options: Remove Account Password, Reset Account Password, Delete Windows Account, or Create Windows Account.
- Select the desired option.
- Additionally, choose the User Account on which you want to apply the function.
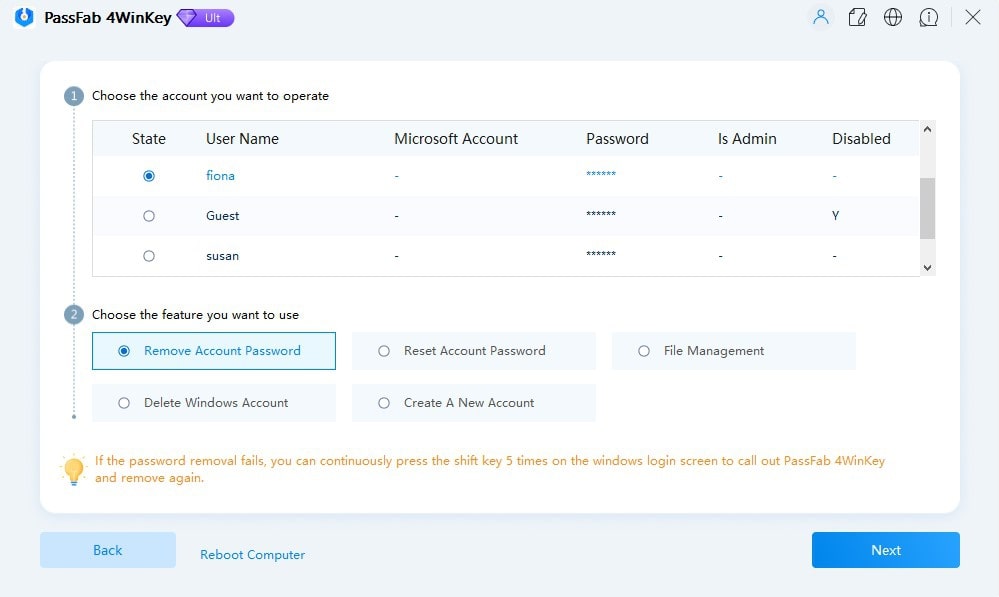
- After selecting the desired option, choose Next to proceed.
- Wait till the PassFab 4WinKey removes the Windows Account login password.
- Click on the Reboot option.
- And wait for the computer to restart.
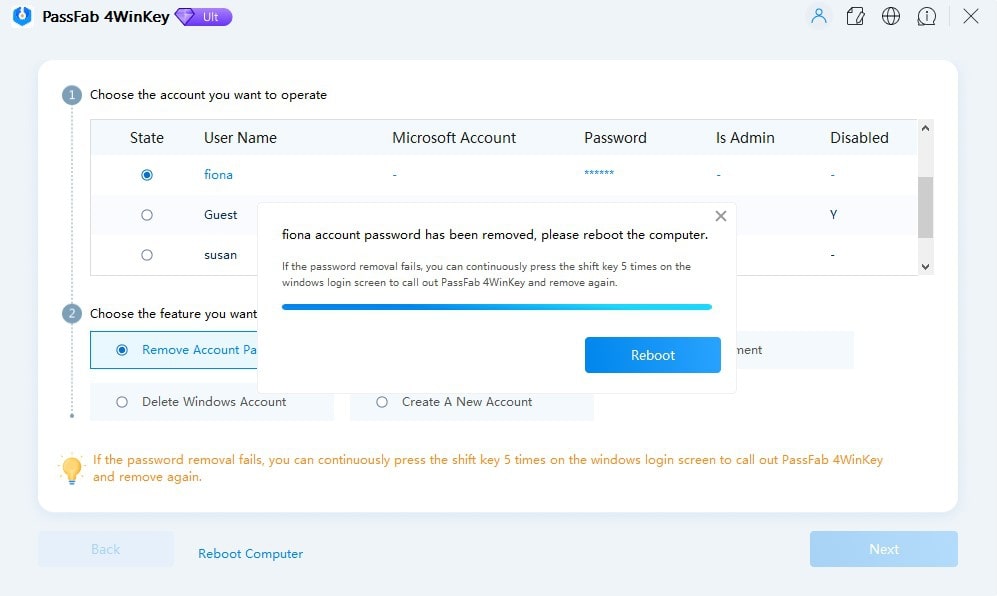
Once the Windows computer restarts, you can log in to the Windows User Account without a password.
Frequently Asked Questions About Hash Format of Windows
1. How is NTLM hashes more secure than LM hashes?
NTLM hashes (the hash format in which modern Windows login passwords are stored in) are more secure than LM Hashes because of length, case sensitivity, salting, and encryption.
The length of the NTLM hashes is 128-bit hashes, while LM hashes are only 56-bit hashes. The NTLM hashes are case-sensitive, whereas the LM hashes are not.
Although NTLM hashes are not immune to attack, they have stronger encryption than LM hashes.
2. What is the weakness of NTLM hash?
NTLM hashes, the hash format in which the modern Windows login password is stored, have advanced features like salting and message signing. This makes it difficult for attackers to recover the lost password.
However, NTLM hashes are vulnerable to dictionary attacks and rainbow tables. They should not be the sole method of protection of sensitive information.
3. Are rainbow tables less effective the more potential characters there are?
Yes. The more potential characters, the larger will be the number of possible passwords. Rainbow tables work by precomputing hashes for the number of potential passwords and storing them in a table.
When a password hash is obtained, the attacker can simply look up the corresponding password and use it to obtain the password of the locked Windows account. But if the password has many characters, the precomputation increases exponentially.
4. How to disable any running antivirus software and turn off the Windows firewall?
To install Cain and Abel and Ophcrack on your Windows computer, you have to disable the Windows Firewall as well as third-party antivirus programs. These programs access the deep trenches of the operating system that a typical software wouldn’t do. As a result, Windows will not allow you to install the program unless you disable the firewall.
Here’s How to Disable Windows Firewall and other Running Antivirus on your computer:
- Go to the Control Panel.
- Choose System and Security.
- Select Windows Firewall.
- From the left pane, select Turn Windows Firewall On or Off.
- Click on the toggle assigned to “Turn Windows On or Off to disable the firewall.
After disabling the Windows Firewall, you can install Cain, Abel, and Ophcrack to reset the Windows password using Hash.
5. How to Reset Windows Login Password Without Hash or Tool?
You can use the Windows installation disc to reset the Windows login password without a hash or tool. Here’s how to do that:
- Boot the locked Windows computer using the installation disc.
- On the Windows Setup screen, press Shift+F10.
- In the command prompt window, type “diskpart” and press Enter. This will open the DiskPart utility.
- Type “list vol” and press Enter to see the list of all volumes on the locked Windows computer. Recognize the volume on which Windows OS is installed.
- Type “exit” to close the DiskPart utility.
Now type the following command:
cd C:\Windows\System32Press Enter to change the system directory.
After changing the System 32 directory, type the following command to make a backup of the ultiman.exe file:
copy utilman.exe utilman.exe.bakAnd type the following command to replace the ultiman.exe file with cmd.exe:
copy cmd.exe utilman.exe- Restart the computer after replacing the ultiman.exe file with the cmd.exe file.
- Once the computer restarts, click on the Ease of Access button on the Windows login screen. Since we have replaced the Ease of Access options with the Command Prompt, you must see the cmd window.
- In the Command Prompt window, type “net user” and press Enter. This will show you the list of all user account on the locked Windows user account.
- Type username (the real user name) and press Enter.
- Type a password of your choice and press Enter.
Use the created password to log in to the locked user account.
6. How much time does it take for the modern Windows hash format to crack?
The cryptanalysis report of 8 character password stored in NTLM hash format (used by the modern Windows login) takes up to 6 hours to crack.
Conclusion
As mentioned, the modern Windows login passwords are stored in NTLM or NT hash format. At the same time, the older version of Windows login passwords is stored in LM hash format. Depending on the hash format used by the Windows version, you can download the Rainbow Tables and use Cain and Abel or Ophcrack to reset the forgotten Windows password.
Of course, finding the original password with a hash is a long and complex process. Plus, it is a highly coordinated process — you must have another user account on the computer, download the relevant rainbow tables, and so on. If you are lucky, i.e., the Windows password is easy, the hash can help you recover the forgotten password. At the same time, the chances of recovering the password are grim. So, if you cannot reset the Windows password using hash, use hash alternatives like PassFab 4WinKey. You can also try resetting your Windows password using the installation disc.
